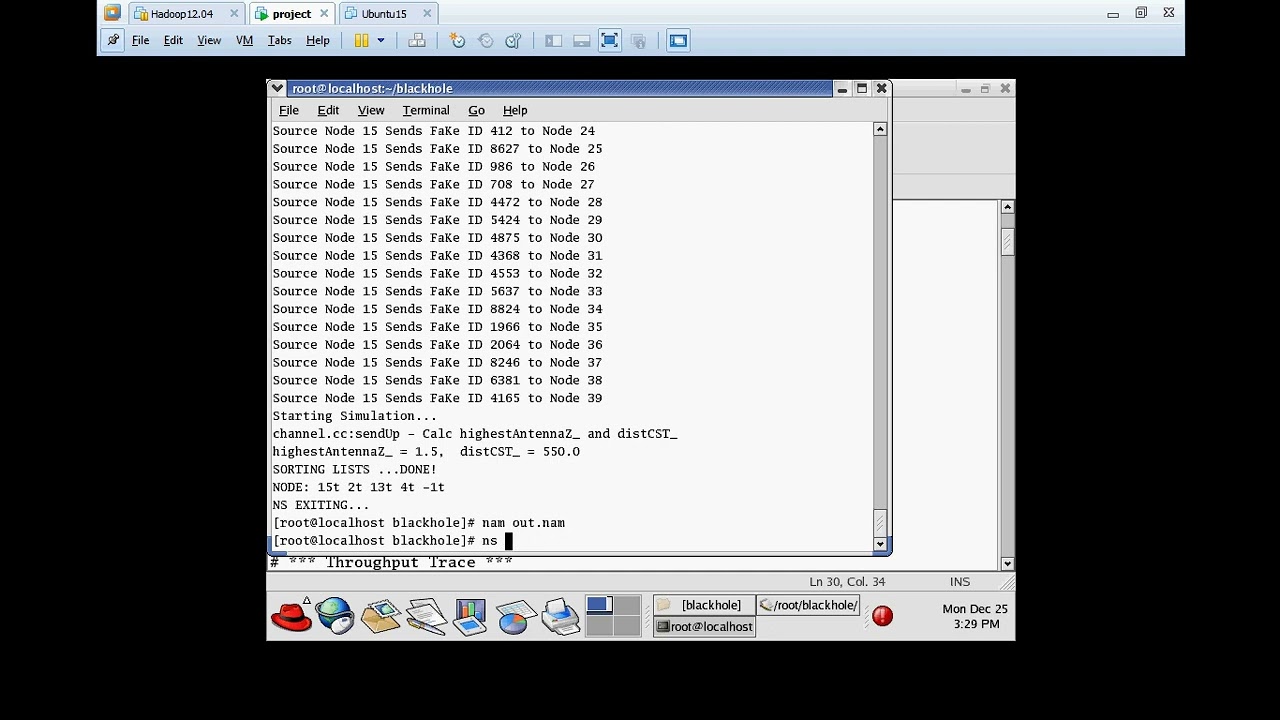
Blackhole Attack detection and Mitigation in NS2 simulation
Introduction
In today’s interconnected world, wireless networks play a pivotal role in facilitating seamless communication and data exchange. However, with the benefits of these networks come security risks, including the notorious “Blackhole Attack.” In this post, we will delve into the world of Blackhole Attack detection, exploring the threats it poses and the cutting-edge techniques to safeguard your network.
Understanding Blackhole attack
A Blackhole Attack occurs when a malicious node within a wireless network deceives other nodes by falsely claiming to have the shortest path to the destination. Instead of forwarding data packets as expected, the attacker drops them, creating a virtual “black hole” that swallows data. This can lead to severe consequences, such as data loss, network congestion, and compromised communication integrity.
Key challenges in Blackhole detection
Detecting Blackhole Attacks is a formidable task due to their deceptive nature. Attackers disguise themselves as legitimate nodes, making it difficult to distinguish their malicious behavior from normal network behavior. Moreover, these attacks can be launched in various wireless network types, such as MANETs and WSNs, adding complexity to the detection process.
hy dear can i got the source code on detection and prevention on black hole attack in AODV